
Oculus VisionTech has developed Document Watermarking Protection technology that is provided as a Cloud service –
Cloud-DPS.
Cloud-DPS is a system made to protect and authenticate digital documents from tampering. It is meant for documents at the end of the editing cycle.
The document tamper-proofing is done in two steps:
- Watermarking creates a “protected copy”, which becomes the true master document. This master document is carried within the file so there is no need to use external sources for verification.
- The authentication process can ascertain whether a document is protected and has not been tampered with by comparing to the protected copy.
Cloud-DPS offers three document services from the Cloud:
- Protection – Accept any incoming document, watermark and return the watermarked
document as an encrypted image-based PDF document - Authenticate – Validate the authenticity of the protected documents
- Storage – Storage of the master protected document in a digital
Cloud-DPS also creates Visible Watermarks (QR Codes)
- Timestamps and Page Numbers
- Psychological Inhibitor
Trying to decide where Cloud-DPS might fit for your company? The system has been used in a variety of ways by companies spanning a vast variety of industries. Take a look at some specific use cases of how the system has been used in the past.
Use Cases for Cloud-DPS
Individual Legal Contracts
Companies use Cloud-DPS for any documents that have a legal component. This can range from sales to employment contracts. Cloud-DPS is a useful tool for individuals looking to protect themselves from tampering and also for professionals such as real estate agents who manage these documents on a daily basis. With the Oculus VisionTech multi-level protection system in place, you can ensure that any document you deal with is the true and original document.
Corporate Contracts
Corporate contracts are big money. The slightest change to a document could mean millions of dollars lost. Cloud-DPS protects these documents to ensure that tampering can not be carried through. Companies of all sizes can use Cloud-DPS to easily protect their valuable documents from tampering.
Engineering Specs Protection
When engineering blueprints need to be shared, it is important that they are protected to ensure that all parties are receiving the original document. The encryption function in Cloud-DPS helps ensure that only authorized people can view the document. Furthermore, if tampering does occur, the digital watermarking features help ensure that all alterations are found. This will allow all parties to have full confidence that what they are viewing is completely authentic. Our proprietary DocuTrace technology was built specifically to prevent unauthorized people from viewing sensitive documents, making it very valuable for engineering specs protection as well.
Other Cases
Here are a some other use cases for the Cloud-DPS:
- Healthcare Records Management System
- Financial Institutions
- High Security Organizations
- Will Management
- 3D Printed Product Protection
- Law Enforcement (Forensics)
- Government Documents
- Copyright Protection
Cloud-DPS
Cloud-DPS is built on two main processes, protection and authentication. Protection changes documents into image based files that include multiple level of security. This includes encryption, edit-locking, watermarking, and a state of the art onboard master copy system. Authentication is the process of checking the in document master copy to ascertain the authenticity of a document.
System Front-End (Oculus Document Watermarking App)
- User Registration Service
1. After installation – register user with billing information. - Document Watermarking Service
1. Collect document from user and dispatch to Oculus web portal for watermarking. - Document Authentication Service
1. Collect document from user and dispatch to Oculus web portal for authentication.
2. Return the result of authentication – genuine or tampered.
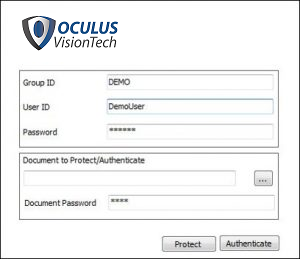
Cloud Document Protection System App
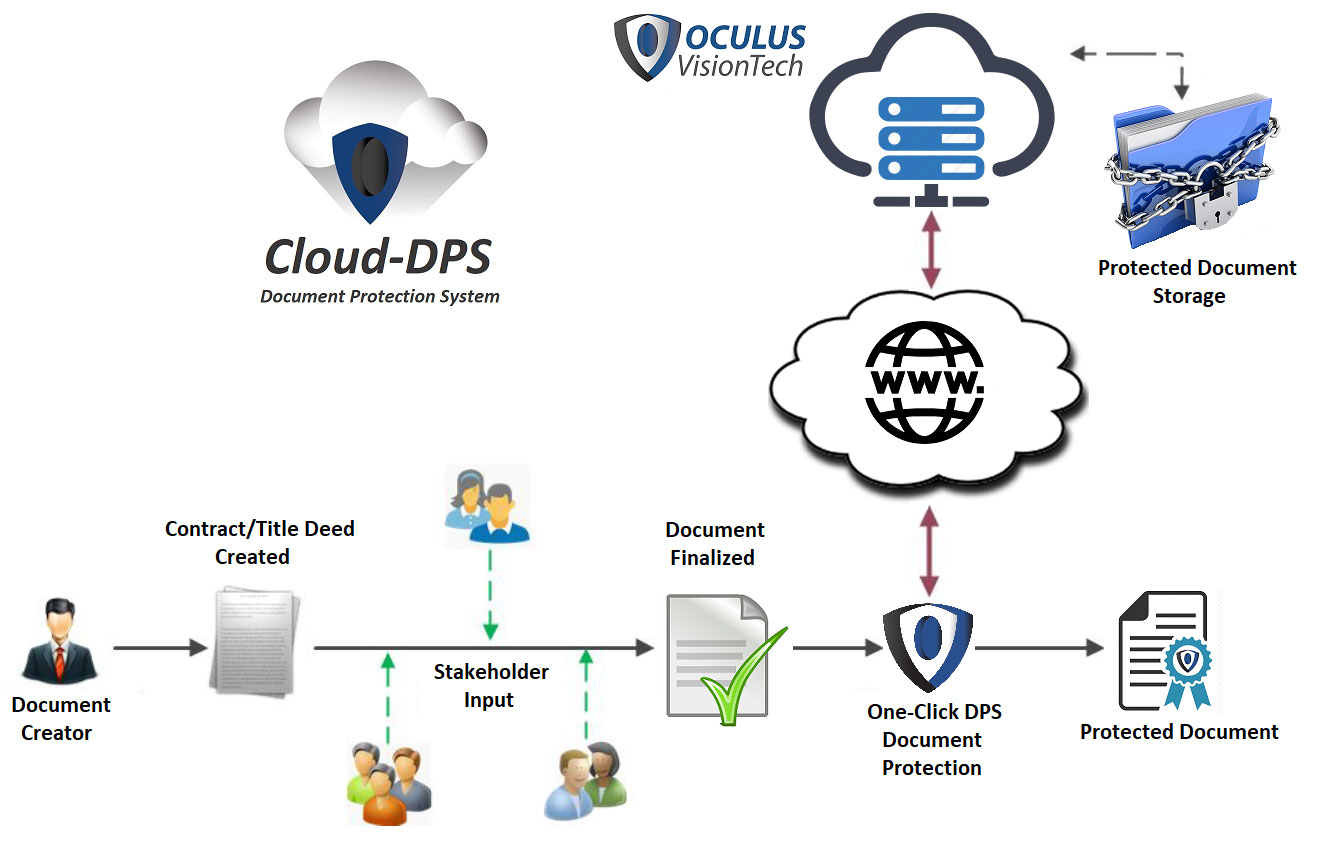
Protection Workflow
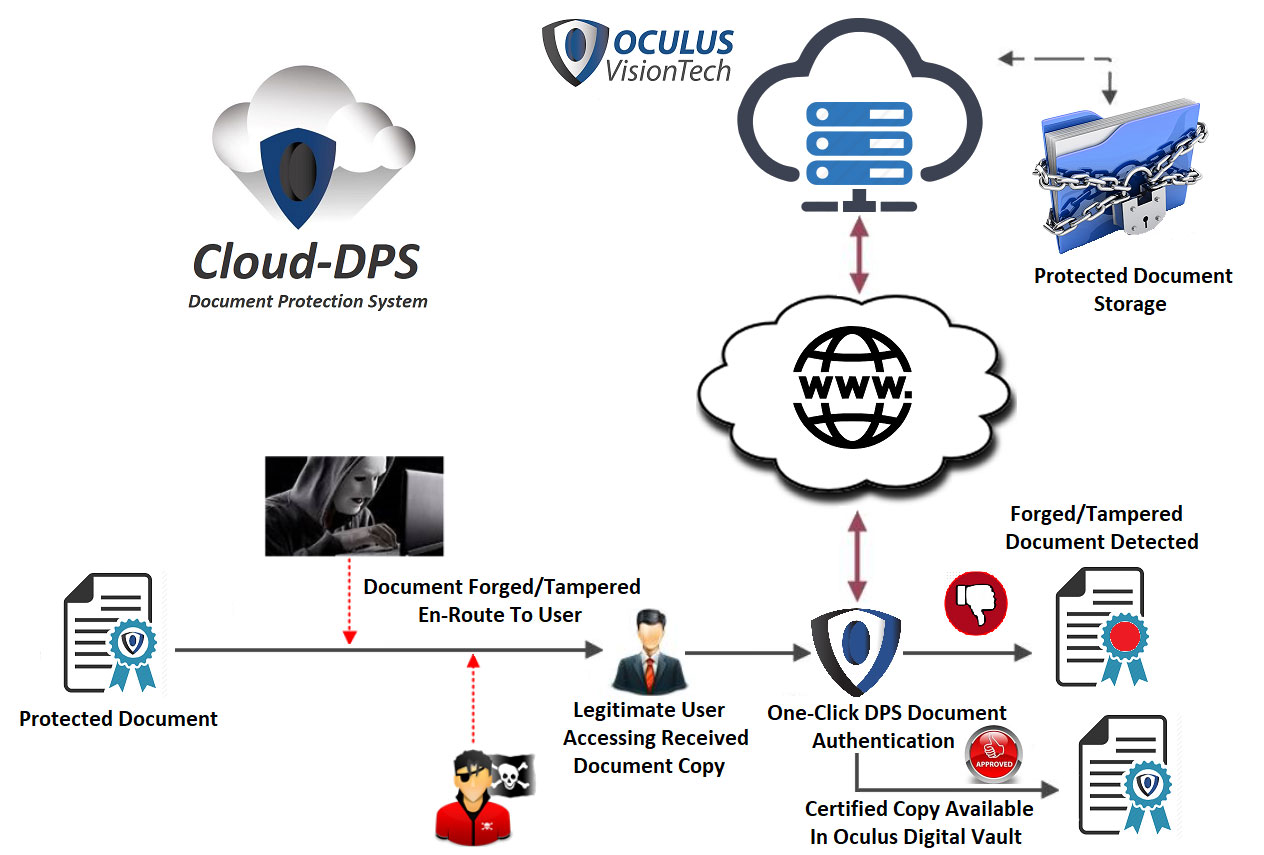
Authentication Workflow
Oculus VisionTech Anti-Tampering Technology
The Anti-Tampering Technology is the core technology in Cloud-DPS. Using proprietary forensic watermarking techniques developed by Oculus VisionTech, this technology creates multi-tiered protection for documents. The Anti-Tampering powers the protection and authentication functions of Cloud-DPS.
Features of the Anti-Tampering Technology
Imperceptible Forensic Watermarking: The Anti-Tampering technology watermarks documents both visually and non-visually. The non-visual watermarking occurs by converting all documents into image-based PDFs. The conversion is done through a powerful image processor that marks down key characteristics of the document that can be checked for authenticity. This form of watermarking allows for the smallest change in the document to be identified.
Visual Watermarks: All documents protected through Cloud-DPS is visually watermarked with QR codes and company logos. There is a QR code that is placed at the bottom of every page that depicts the page numbers and a timestamp of the time of protection when scanned. There is also another QR code at the bottom of the document that shows the individual document code when scanned. These timestamps and code identifiers are used as added security for document users to ensure authenticity.
On-Board Master Document: The master document that hosts the key characteristics used to check authenticity is hosted within the PDF file, making it verifiable offline and online. By creating a completely autonomous verification system, Cloud-DPS avoids any tampering that can occur during authentication through document interception.
Encryption: All documents protected through Cloud-DPS are password protected and read only. Furthermore, protection can only be completed by verified users with proper credentials and system administrators. This first step of protection allows for control over document access from the protection to viewing.
Authentication: The state of the art authentication system within Cloud-DPS can identify even the smallest changes to a document . The Anti-Tampering technology will notify users of any tampering that has occurred and show the exact location where the authentication has failed. This level of authentication gives users security and insight never before seen in anti-tampering software.
Learn More
Demo
For a demo click here.
